Secure by design in Mendix: from reactive security to built in control
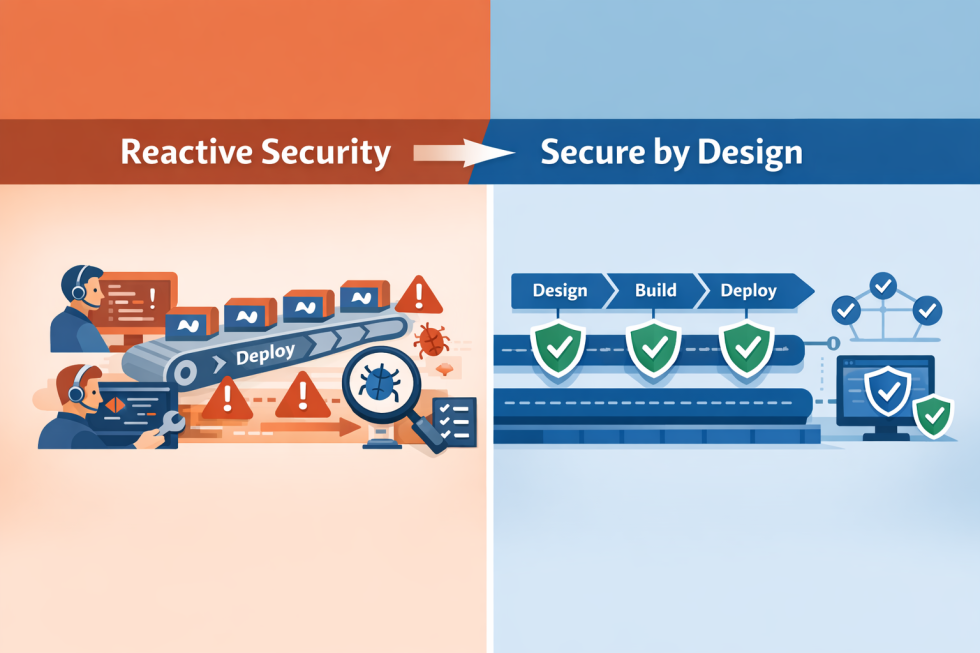
Security in many organizations still operates as a reactive function. Vulnerabilities are discovered after applications are deployed and incidents trigger investigations. Security teams then respond with patches, additional controls, or process adjustments. This model worked when software changed slowly and application landscapes were relatively small, but it is far less effective in modern low code environments.
Mendix applications evolve continuously. New features are deployed frequently, teams work in parallel across multiple applications, and integrations expand over time. In such an environment security that relies primarily on reacting to discovered problems becomes increasingly difficult to manage. The challenge is therefore no longer simply identifying vulnerabilities. The real challenge is ensuring that the conditions in which vulnerabilities can arise remain structurally under control. This shift defines the principle of secure by design.
Security as a design property
Traditional security approaches often treat security as a review phase. Applications are developed first and security validation takes place afterwards through testing, audits, or vulnerability scans. The problem with this model lies in the timing. By the time a vulnerability is discovered, the design decisions that allowed it may already be deeply embedded in the application architecture. Correcting the issue can require structural changes that are costly and disruptive.
Secure by design approaches the problem differently. Instead of identifying vulnerabilities after they appear, the goal is to structure systems so that many categories of vulnerabilities cannot easily occur in the first place. Security therefore becomes a property of the system’s design rather than a reaction to discovered weaknesses.
Why Mendix already provides a strong foundation
The Mendix platform naturally supports several principles aligned with secure by design. The platform introduces clear abstractions around data models, access control, and deployment boundaries. Domain models define the structure of application data and access rules determine which roles can interact with specific entities or pages. Deployments occur within a controlled runtime environment. These characteristics provide a strong foundation.
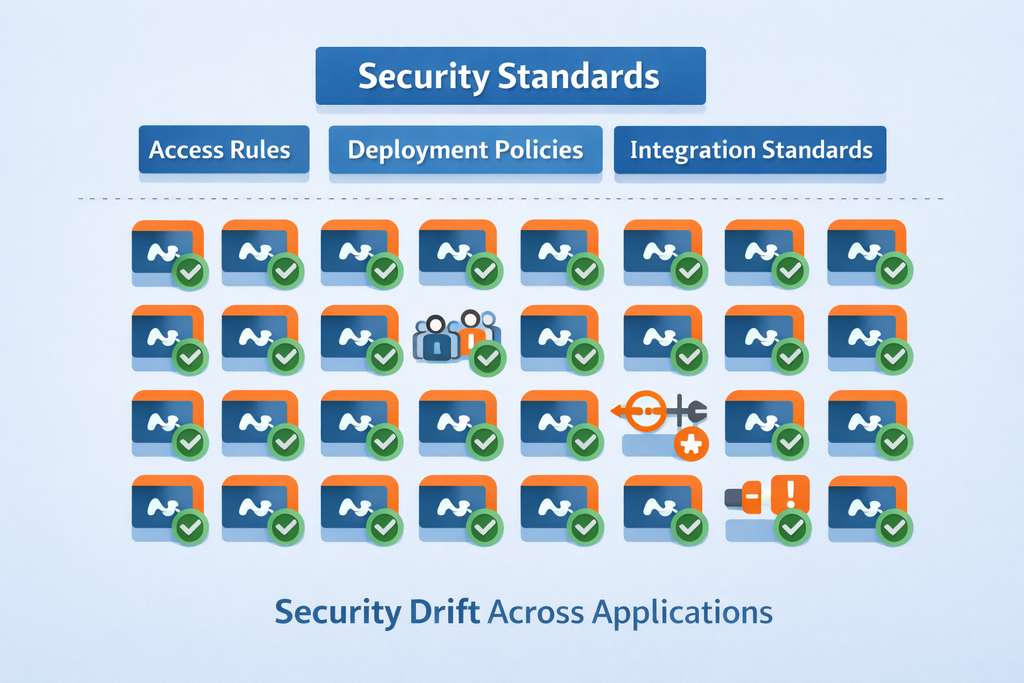
However, the platform alone does not guarantee secure outcomes. As Mendix landscapes grow, organizations often manage dozens or even hundreds of applications. Multiple development teams contribute to the environment, dependencies between applications increase, runtime configurations evolve, and operational complexity grows. At that point the challenge shifts from securing individual applications to maintaining consistent control across the entire application portfolio.
The acceleration problem
Low code accelerates development. That is precisely why organizations adopt platforms such as Mendix. However, speed also introduces new risks. When building applications becomes easier, the number of applications grows rapidly. Teams may implement similar functionality in different ways and security policies may be interpreted differently across projects. Configurations between environments can diverge and small deviations accumulate over time. Eventually the security posture across the landscape becomes inconsistent. What started as a design challenge gradually becomes a governance challenge. Secure by design requires organizations to address this reality directly.
Integrating security into the lifecycle
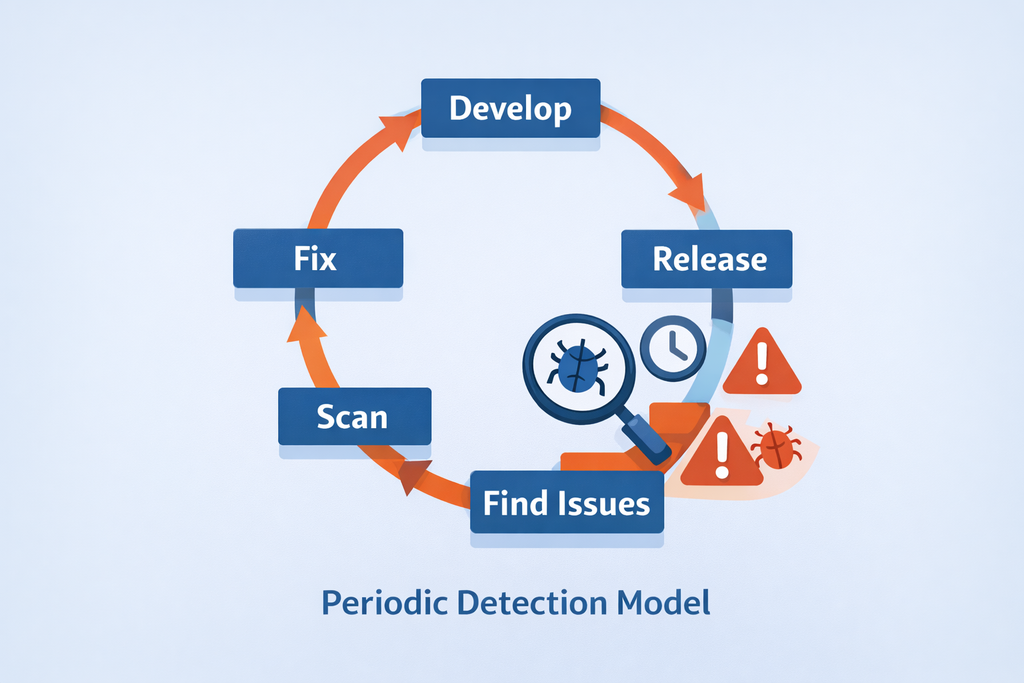
In mature Mendix environments security cannot remain a periodic review activity. It must become part of the development lifecycle itself. Instead of evaluating security only after deployment, applications are continuously assessed against defined policies and standards.
This model typically includes several characteristics:
- security policies are explicitly and consistently defined
- applications are automatically evaluated against those policies
- deviations become visible immediately
- remediation can occur quickly while the context of the change is still fresh
The result is not slower development. Development can continue at high speed while maintaining structural control. Security becomes an operational property of the platform rather than an after the fact intervention.

From policy to operational control
Many organizations already have security policies in place. That is a necessary first step. However, policies written on paper do not enforce themselves. When verification occurs only through manual reviews or occasional audits, compliance remains fragile. Effective governance requires operationalizing those policies.
In practice this means that:
- policies are translated into automated checks
- the state of applications is evaluated continuously
- evidence of compliance is generated automatically
- exceptions become visible as soon as they occur
Control therefore becomes continuous rather than periodic.
Security as a governance capability
Secure by design ultimately intersects with governance. Organizations must be able to demonstrate that their systems remain within defined security and compliance boundaries, not only during audits but at any moment in time. This requires visibility. Platform teams need to understand which policies apply, which applications are evaluated against those policies, where deviations occur, and how those deviations are resolved. Without this visibility governance remains reactive. With it governance becomes operational.
The broader implication
As Mendix adoption expands within organizations, the central question evolves. It is no longer only about whether individual applications are secure. The question becomes whether the entire Mendix landscape remains structurally within control boundaries as it continues to grow. Secure by design provides the conceptual framework to answer that question. Not by reacting faster to vulnerabilities, but by structuring systems so that many vulnerabilities never emerge in the first place. When this approach is combined with continuous governance and automated policy evaluation, organizations gain something many still lack today: continuous control.


